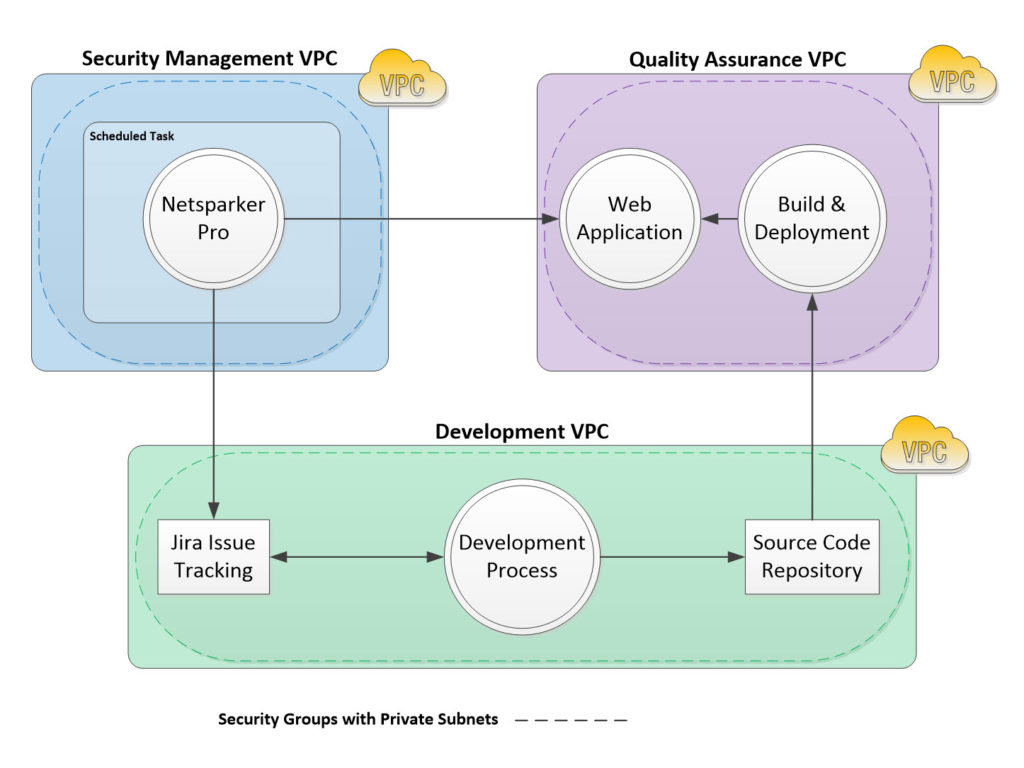
The above high-level data flow diagram illustrates a custom-solution we developed for a client who has migrated their software development environment and production applications to Amazon Web Services (AWS).
Many organizations are migrating their software development, quality assurance (QA), and production environments to Amazon Web Services (AWS). Netsparker Professional Desktop can be deployed in this environment to scan applications in both QA and Production. The scanning can be automated and vulnerabilities can be manually submitted to an issue tracking system. The above diagram is an example of how to deploy Netsparker Professional for automated scanning of a Web Application in QA.
- Netsparker Professional is installed on an EC2 instance in the Security Management Virtual Private Cloud (VPC).
- The Web application to be scanned is located in a QA VPC with its supporting build and deployment systems.
- A Jira issue tracking system is located in the Development VPC.
- The VPCs are initially configured with private IP addresses and Security Groups that do not allow inbound access. The connection from the Security Management VPC to the QA VPC; and Security Management VPC to Development VPC is configured with VPC peering. “A VPC peering connection is a networking connection between two VPCs that enables you to route traffic between them using private IP addresses. Instances in either VPC can communicate with each other as if they are within the same network. You can create a VPC peering connection between your own VPCs, or with a VPC in another AWS account within a single region.”1
- A scheduled task in Windows executes a batch file that launches Netsparker, scans the Web application in the QA environment, generates a detailed scan report2, and sends an e-mail notification when the task is triggered, and upon completion.3
- If there are any vulnerabilities, they can be submitted directly to Jira from Netsparker using the “Send To Action” feature.4
References:
1 – http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/vpc-peering.html#create-vpc-peering-connection
2 – https://netsparker.zendesk.com/entries/121421-reading-target-websites-from-a-text-file
3 – https://technet.microsoft.com/en-us/library/cc748993.aspx
4- https://www.netsparker.com/blog/docs-and-faqs/integrate-netsparker-web-security-scanner-bug-tracking-system/
